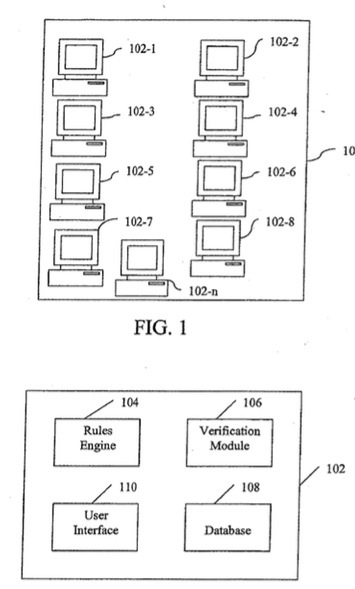
An Apple patent (number 20120278863) has appeared at the U.S. Patent & Trademark Office for ad hoc account creation. It provides a mechanism that allows a user to easily configure a rules engine to apply rules to decide which requests for access to a user’s computer resources are to be granted and which are denied.
Per the patent, a trusted token, such as a certificate of identity issued by a trusted third party authority that verifies identities of computer users, is included in a calling card object provided by the requesting user to the (server) computer that controls the resources desired by the requester. Additional conditions for access may be specified as desired by the user of the server computer.
Here’s Apple’s background on the invention: “Proliferation of portable computers and computer networks has drastically widened the scope of computer usage for the average computer user. Access to computer networks is now offered in such public venues as coffee shops, hotels, and other places where people connect to a network in a casual or ad-hoe manner, for example, a one-time connection or multiple connections over a brief period. However, establishing connections between individual computers connected in this ad-hoc manner has not evolved with this expanded access.
“For online communication, individual users still must use third party resources, such as websites that host multiple users, to share resources or even to facilitate communication. In these conventional resource-sharing environments, a user must still establish an account through a largely mechanical process on the client end, where a user approaches a website by first asking for an account to be created, and then engaging in a dialogue where the user either supplies a username and password, or is assigned the username and password from the server asked to create an account.
“As computing power has evolved, even the simplest of computers sold today can function as servers and distribute computing resources and assets to other computers. However, the average computer user has no easy way to validate the identity of another user requesting access, and ad-hoc user account creation suffers a serious shortcoming from the perspective of security. There also is no simple way for one computer to share resources unless either a third party entity is involved, or the computer users manually share resources.
“Most computer users are not interested in performing manual account creation for everyone who wants access to his or her computer resources. Also, varying levels of scrutiny to access requests currently are insufficient for the average user. Where an individual user may not require a high level of scrutiny for someone wishing to access a collection of stored computer images or photographs, a higher degree of security may be desired for more sensitive information that a computer user may only wish to share with select individuals.
“Thus there remains a significant need for a mechanism for computer users that provides security and automation in a resource-sharing environment that is easily configured by a user.”
The inventors are Leland A. Wallace and David M. O’Rourke.