The coronavirus/COVID-19 outbreak, in addition to the health and economic threats if posed, has also resulted in the birth of a cybersecurity threat, igniting a bevy of COVID-19-themed phishing lures and newly registered COVID-19-related domains that promise information about COVID-19. In fact, this could well be the biggest-ever cybersecurity threat.
Check Point’s January Global Threat Index shows cyber-criminals are exploiting interest in the global epidemic to spread malicious activity through several spam campaigns relating to the outbreak of the virus For example, CNN.com hosts over 1,200 articles mentioning the disease, and a search on the website of The Financial Times produces over 1,100 results.
Since January 2020, based on Check Point Threat Intelligence, there have been over 4,000 coronavirus-related domains registered globally. Out of these websites, 3% were found to be malicious and an additional 5% are suspicious. Coronavirus- related domains are 50% more likely to be malicious than other domains registered at the same period.
Many of these domains will probably be used for phishing attempts. As of now, Check Point say it’s already spotted and protects online users from many websites known to be related to malicious activities that lure the victims to their websites with discussions around the virus, as well as from scam websites that claim to sell face masks, vaccines, and home tests that can detect the virus. However, while the primary threat is related to phishing, security researchers have found malware such as Trojans and worms disguised as educational documents that can steal data.
Cybersecurity firm Recorded Future recently studied the coronavirus cybersecurity threat. Its report finds:
- As of March 11, 2020, COVID-19 has been primarily used by cybercriminals as a theme for phishing lures. However, we have observed at least three cases where reference to COVID-19 has been leveraged by possible nation-state actors. Recorded Future feels that as the number of COVID-19 cases, as well as publicity around the virus, rises globally, both cybercriminals and nation-state actors will increasingly exploit the crisis as a cyberattack vector.
- Cybercriminals will often use the branding of “trusted” organizations in these phishing attacks, especially the World Health Organization and U.S. Centers for Disease Control and Prevention, in order to build credibility and get users to open attachments or click on the link.
- The number of references to COVID-19 in relation to cyberattacks has increased over the last two months, including country-specific phishing lures as the virus becomes more prevalent in that country. Recorded Future assesses that, for the duration of the outbreak, COVID-19 will continue to be used as a lure, and that new versions of these lures targeting new countries will emerge.
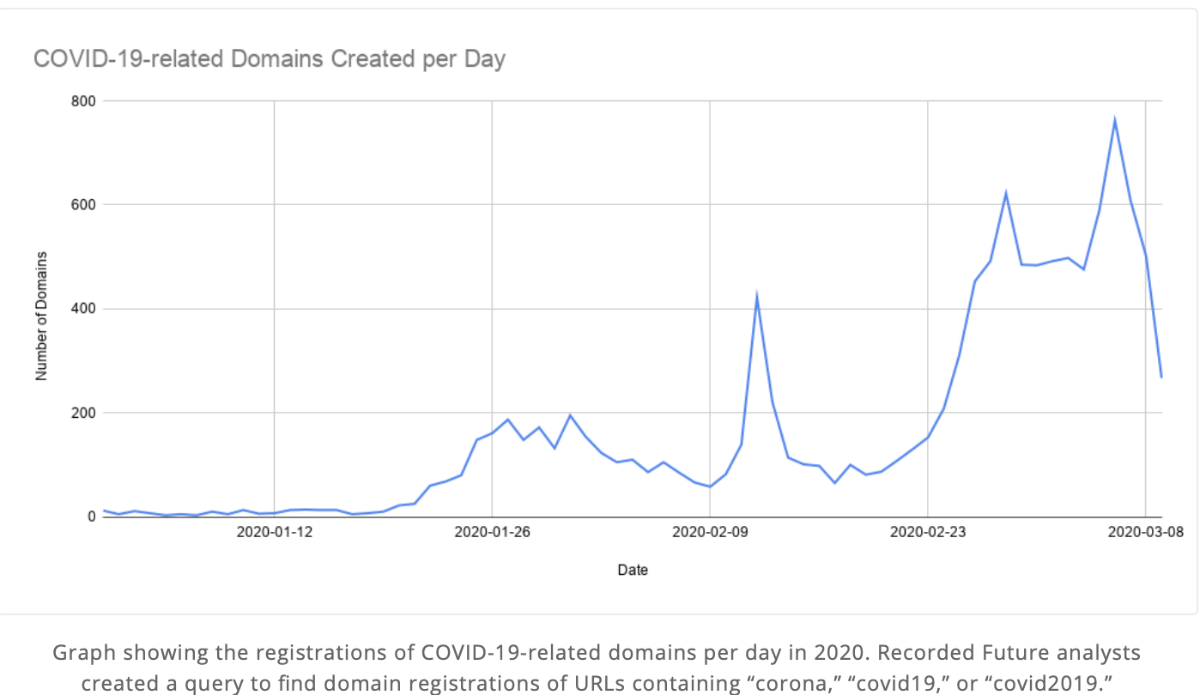
- The number of newly registered domains related to coronavirus has increased since the outbreak has become more widespread, with threat actors creating infrastructure to support malicious campaigns referring to COVID-19. The initial spike in domain registrations coincided with a large spike in reported COVID-19 cases in mid-February — a possible indicator that attackers may have begun to realize the utility of COVID-19 as a cyberattack vector.
Recorded Future recommends that organizations should take the following precautions:
- Be especially wary of any email or other communications purporting to come from the CDC or WHO, even if it appears to come from a legitimate address on the official domains (cdc[.]gov and who[.]int). Many of the phishing emails used the branding and trademarks of these two organizations as part of the lure, and this trend will likely continue as the outbreak grows in the United States. Threat actors have also incorporated URLs with legitimate websites as the link text, while the underlying link is malicious. The U.S. Federal Trade Commission has suggested that interested parties visit the known WHO and CDC websites directly for up-to-date information and to be cautious about any email purporting to be from those entities. Unless your organization is in the healthcare field, it is unlikely that these agencies will be sending you emails about COVID-19. Also note that the CDC, WHO, and other organizations do not take cryptocurrency payments, so any request of this type should be considered malicious.
- While many legitimate organizations will send emails regarding precautions that they are taking to minimize the threat of COVID-19, the use of legitimate corporate branding has been used to send malware to victims. The malicious emails often use language creating a sense of urgency (though often with bad grammar or spelling), or attachments or links that are said to contain additional information rather than being informational themselves. Users should avoid opening attachments, but it is advisable to treat all emails regarding the COVID-19 outbreak with caution.
- As with all phishing attacks, it is recommended that users disable macros in Microsoft Office for any users that do not absolutely require it. Many of the malicious attachments observed by Recorded Future analysts in association with COVID-19 used VBA macros as an initial part of the infection of victims. VBA macros remain popular infection mechanisms for malicious documents that are used as phishing lures, and analysts assess with high confidence that this trend will continue.
Employees that work from home often use their personal computers which are usually less secure than the organizational ones, making them more vulnerable to malware attacks.
While 21% of these emails featured simplistic attacks with a link to download a malicious executable embedded in the email body, the vast majority included more advanced capabilities such as malicious Macros and exploits or redirection to malicious websites – a challenge that surpasses the capabilities of most AV and email protection solutions, according to the Cynet security firm.
“The fact that only about 10% of the malware in these attacks was identified by its signature, indicates that the attackers behind these campaigns are using advanced attacking tools to take advantage of the situation,” says Eyal Gruner, CEO and co-founder of Cynet.
As a breach protection platform, Cynet introduces a dedicated offering tailored to the new Coronavirus related cyber risks.
- For both existing and new customers, Cynet will allow, free of charge (for six months), the deployment of its product, Cynet 360, on personal computers used by employees working from home.
- Cynet massively adds staff to CyOps, its MDR services team, to be able to cover for companies with reduced security staff because of the Coronavirus.
What’s more, Norton offers seven tips from working from home in these difficult times:
Keep close contact with your employer. It’s smart to stay on top of company communications. Your inbox might contain emails about policy changes ranging from work hours to travel. Your employer might consolidate coronavirus-related information on the company intranet. If you have questions, ask.
Companies around the world continue to react to developments around the COVID-19 pandemic. It’s important to know new policies to help keep you, your coworkers, and the business safe.
Use what’s in your company’s tech toolbox
Companies often have tech tools that can help keep you cybersafe when you work from home. That might mean you do your work on company-supplied laptops and mobile devices. They likely include firewall and antivirus protection, along with security features like VPN and 2-factor authentication.
Your employer’s cybersecurity tools are designed to protect data and devices. Cybercriminals have an interest in both, whether you’re working in the office or at home.
Control the impulse to improvise
Employees often work in teams, and that can mean using collaboration tools like instant-messaging platforms and video-meeting rooms. If a tool isn’t working right, you might be tempted to download a substitute. Don’t do it.
You could inadvertently introduce a software program with a security flaw — and that means someone unauthorized may be able to access company data, or any personal data you have on that device.
Your employer likely has vetted its collaboration tools and makes sure they’re secure. You can’t be sure a quick-fix tool you’ve downloaded has the same protections.
Stay current on software updates and patches. You might get reminders that software updates are available for your computer, laptop, tablet, or mobile device. Don’t wait. Update. Also, keep in mind you can configure your devices to update automatically.
Updates help patch security flaws and help protect your data. Updates can also add new features to your devices and remove outdated ones.
Keep your VPN turned on. A VPN — short for virtual private network — can help protect the data you send and receive while you work from home. A VPN can provide a secure link between employees and businesses by encrypting data and scanning devices for malicious software such as viruses and ransomware.
VPNs help protect against cybercriminals and snoops from seeing what you do online during a workday. That might include sending or receiving financial information, strategy documents, and customer data. A VPN helps keep that information secure from cybercriminals and competitors.
Beware of coronavirus-themed phishing emails. Cybercriminals are exploiting the coronavirus outbreak to send fake emails with dangerous links to employees. Here’s how it works. The email messages may appear to come from company officials and might ask you to open a link to a new company policy related to the coronavirus. If you click on the attachment or imbedded link, you’re likely to download malware onto your device. Don’t click. Instead, immediately report the phishing attempt to your employer.
A phishing email with malicious software could allow cybercriminals to take control of your computer, log your keystrokes, or access sensitive business information and financial data.
Develop a new routine. Working from home requires changing your routine. Making sure you’re cyber secure is part of that. But it also involves structuring your day to work efficiently and maintain contact with your team. If you’re used to starting the day by greeting your coworkers, you might consider continuing to do that by email or on a chat platform.
It’s easy to lose focus or feel isolated when working from home. Take steps to avoid letting that happen. Reach out and stay engaged with your colleagues. The coronavirus may have changed your work life, but you still have a job to do.
Of course, Norton also encourages you to check out Norton Secure VPN, software that allows you “to check email, interact on social media and pay bills using public Wi-Fi without worrying about cybercriminals stealing your private information.”