Arstechnica reports that a code execution bug in s macOS allows remote attackers to run arbitrary commands on your device. An update of the operating system to deal with the issue hasn’t yet been released.
Independent security researcher Park Minchan discovered the vulnerability. Shortcut files that have the inetloc extension are capable of embedding commands inside. The flaw impacts macOS Big Sur and prior versions.
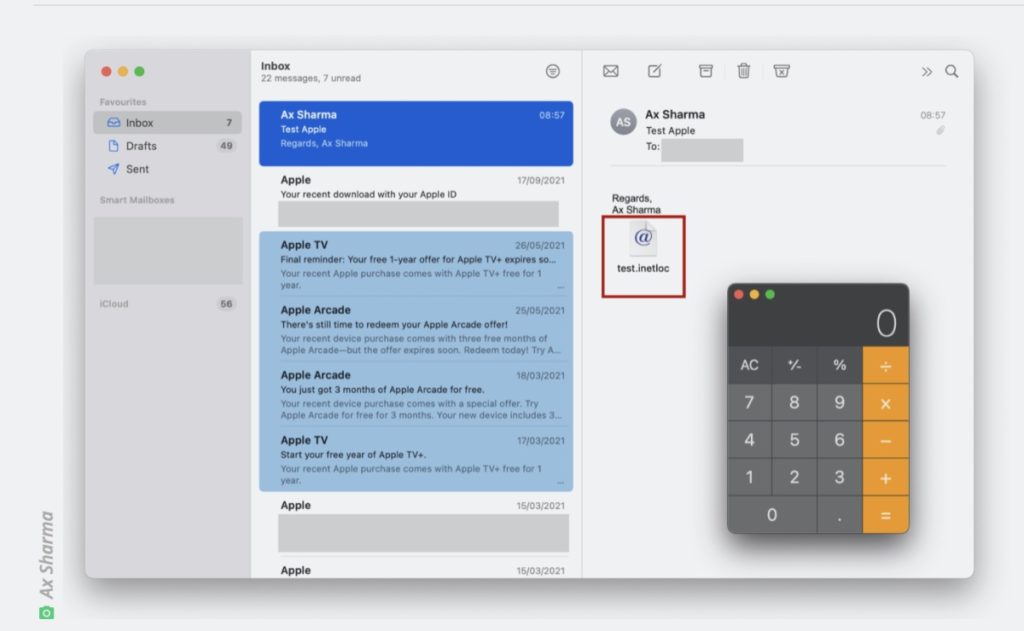
“A vulnerability in the way macOS processes inetloc files causes it to run commands embedded inside, the commands it runs can be local to the macOS allowing the execution of arbitrary commands by the user without any warning / prompts,” Minchan told Arstechnica. “Originally, inetloc files are shortcuts to an Internet location, such as an RSS feed or a telnet location; and contain the server address and possibly a username and password for SSH and telnet connections; can be created by typing a URL in a text editor and dragging the text to the Desktop.”
Although Apple was notified of the flaw and, starting with Big Sur, blocks the inclusion of file:// URLs in Internet shortcuts, one can get around the block by changing the text case, the article adds. Arstechnica warns that “Mac users are warned to be cautious when opening .inetloc Internet shortcuts, especially ones that come in via email attachments.
Article provided with permission from AppleWorld.Today