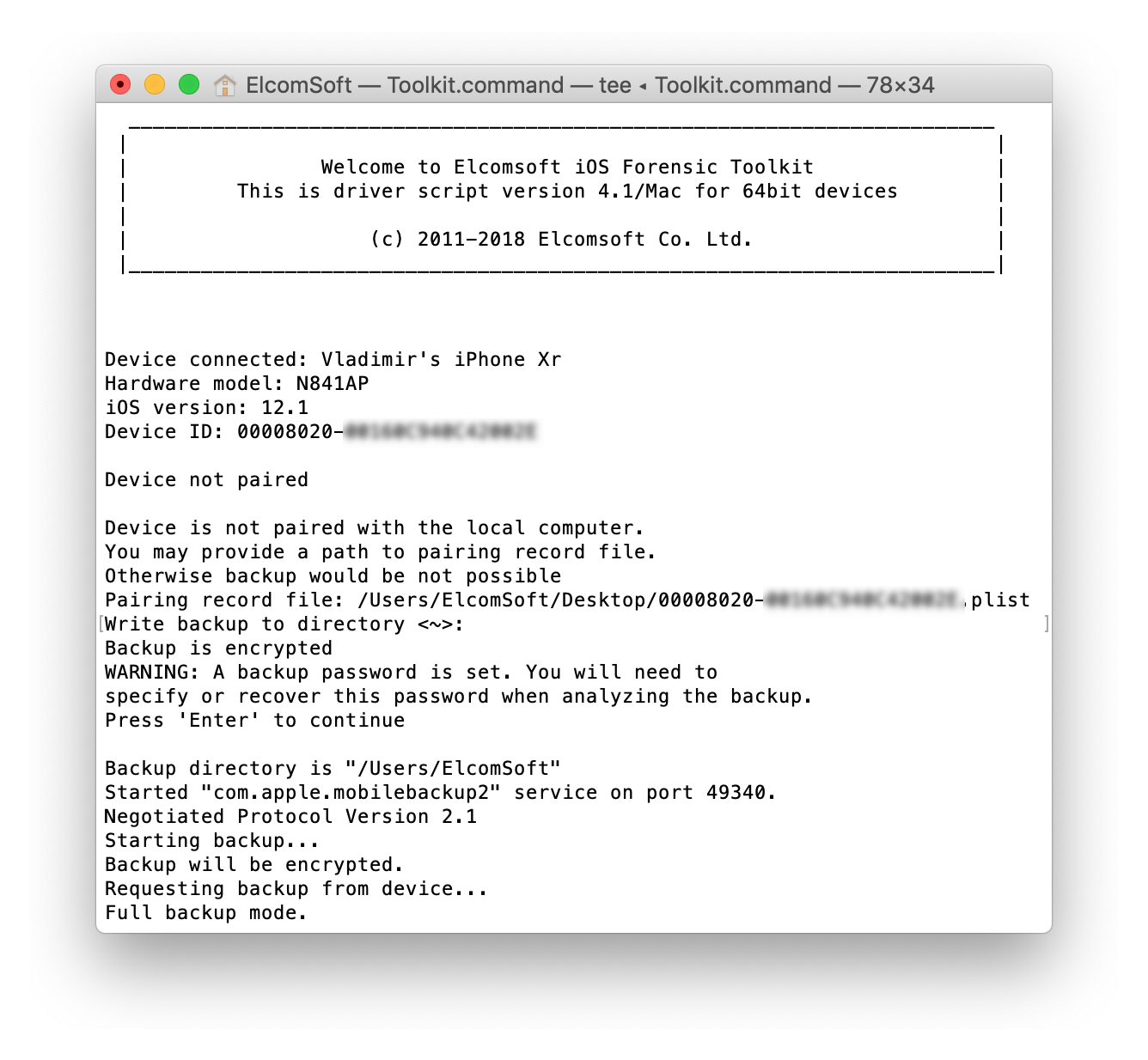
Elcomsoft has updated iOS Forensic Toolkit, its mobile forensic tool for extracting data from a range of Apple devices. Version 5.20 adds the ability to extract the file system and decrypt the keychain from select Apple devices running all versions of iOS from iOS 12 to iOS 13.3.
Partial file system extraction is now possible from locked iPhones even if the screen lock password is not known, says Vladimir Katalov, Elcomsoft CEO. The list of supported devices includes a number of models ranging from the iPhone 5s all the way up to the iPhone X, iPad models from iPad mini 2 to iPad Pro 10.5 and the new iPad (2018), Apple TV HD (ATV4) and Apple TV 4K.
Making use of the new future-proof bootrom exploit built into the checkra1n jailbreak, Elcomsoft iOS Forensic Toolkit can extract the full file system image, decrypt passwords and authentication credentials stored in the iOS keychain, Katalov says. For locked iPhones, the tool offers partial file system extraction.
Extracting Data from Locked iPhones
For the first time, iOS Forensic Toolkit 5.20 supports partial acquisition for BFU (Before First Unlock) devices, as well as for locked devices with unknown screen lock passcode. Targeting a vulnerability in Apple’s bootrom, the jailbreak is installed via DFU mode and is available for all compatible devices regardless of their lock state of BFU/AFU status. As a result, Elcomsoft iOS Forensic Toolkit 5.20 makes it possible to perform partial file system extraction for locked devices as well as devices that are in the USB restricted mode.
Elcomsoft iOS Forensic Toolkit 5.20 is immediately available in Mac and Windows editions. Pricing starts from $1,495. The Toolkit is available stand-alone and as part of Elcomsoft Mobile Forensic Bundle.